|
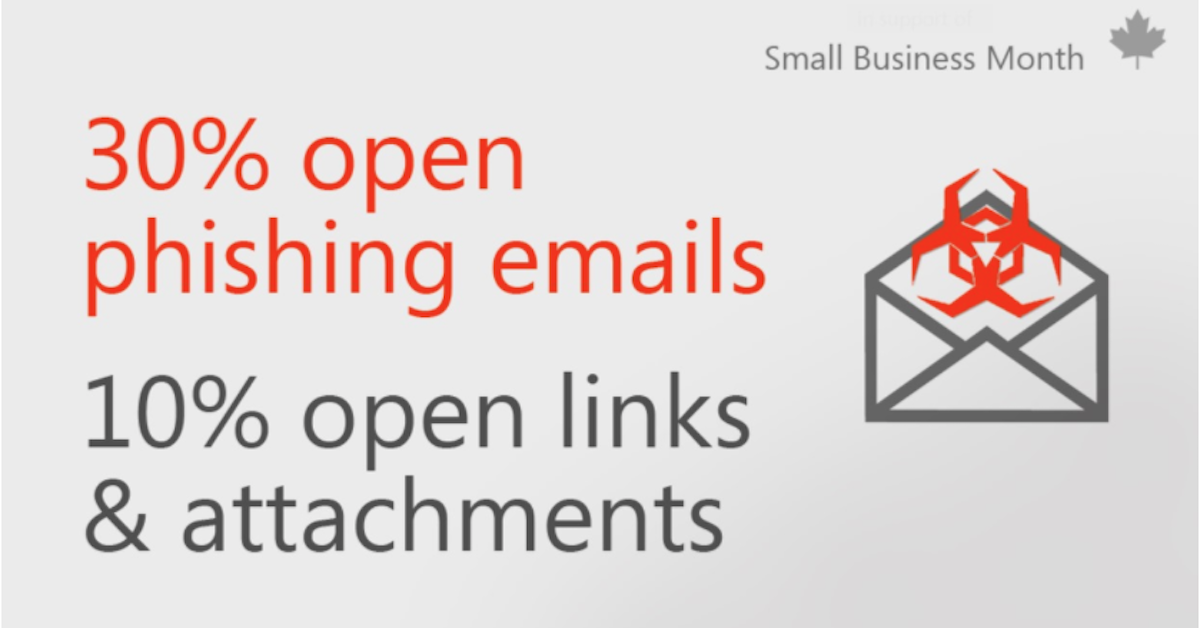
In this article , explore how small businesses can better assesses the risk(s) to them from criminal behavior, include phishing and other cyber-attacks. Then review the scope of activities you need to consider and a checklist you can follow. Categories All Original release date: September 10, 2018
When your computer is accessible through an internet connection or Wi-Fi network, it is susceptible to attack. However, you can restrict outside access to your computer—and the information on it—with a firewall. What do firewalls do? Firewalls provide protection against outside attackers by shielding your computer or network from malicious or unnecessary network traffic. Firewalls can also prevent malicious software from accessing a computer or network via the internet. Firewalls can be configured to block data from certain locations (i.e., computer network addresses), applications, or ports while allowing relevant and necessary data through. What type of firewall is best? Categories of firewalls include hardware and software. While both have advantages and disadvantages, the decision to use a firewall is more important than deciding which type you use.
Most commercially available firewall products, both hardware and software based, come pre-configured and ready to use. Since each firewall is different, you will need to read and understand the documentation that comes with it to determine whether the default firewall settings are sufficient for your needs. This is particularly concerning because the “default” configuration is typically less restrictive, which could make your firewall more susceptible to compromise. Alerts about current malicious activity sometimes include information about restrictions you can implement through your firewall. Though properly configured firewalls may effectively block some attacks, do not be lulled into a false sense of security. Firewalls do not guarantee that your computer will not be attacked. Firewalls primarily help protect against malicious traffic, not against malicious programs (i.e., malware), and may not protect you if you accidentally install or run malware on your computer. However, using a firewall in conjunction with other protective measures (e.g., anti-virus software and safe computing practices) will strengthen your resistance to attacks. Ask us about our Sophos XG Firewall This product is provided subject to this Notification and this Privacy & Use policy. The Federal Bureau of Investigation (FBI) has released an article on building a digital defense against a fraud that uses Facebook’s texting app—Facebook Messenger. Scammers send messages that appear to be from trusted sources or trick users into clicking on malicious links or sharing personal information. Before clicking on links, users should verify the validity of the message with the sender outside of the app. Talk to us about a security assessment!What is a social engineering attack?
In a social engineering attack, an attacker uses human interaction (social skills) to obtain or compromise information about an organization or its computer systems. An attacker may seem unassuming and respectable, possibly claiming to be a new employee, repair person, or researcher and even offering credentials to support that identity. However, by asking questions, he or she may be able to piece together enough information to infiltrate an organization's network. If an attacker is not able to gather enough information from one source, he or she may contact another source within the same organization and rely on the information from the first source to add to his or her credibility. What is a phishing attack? Phishing is a form of social engineering. Phishing attacks use email or malicious websites to solicit personal information by posing as a trustworthy organization. For example, an attacker may send email seemingly from a reputable credit card company or financial institution that requests account information, often suggesting that there is a problem. When users respond with the requested information, attackers can use it to gain access to the accounts. Phishing attacks may also appear to come from other types of organizations, such as charities. Attackers often take advantage of current events and certain times of the year, such as
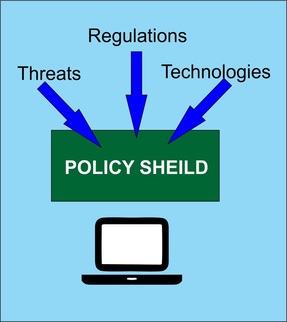 Network Security begins with a set of policies that will define and shape your network security landscape. Once the policies are in place, Silloway Networks can tune your existing hardware and software to enforce your policies. Here is a list of the recommended Security Policies for a small business. General Policy Templates
Network Security
Server Security
Web Application
Developing policies is a fairly daunting task. Silloway Networks can provide 'templates' you can use to develop customized security for your office. Let us know how we can assist you. 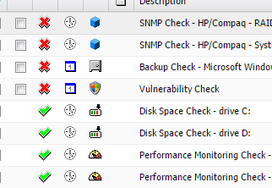 Silloway Network's Sever, Desktop Monitoring and Security Package The companies, law offices, and organizations we support are faced with the challenge of complying with increasingly demanding government regulations; Sarbanes-Oxley PCI/DSS Compliance Health Insurance Portability and Accountability Act (HIPAA) COBIT NIST 800-53 ISO 27001 Gramm-Leach-Bliley Act CJIS Security Policy and more. Many of our clients are already using Silloway Server Monitoring to assist them in fulfilling regulatory compliance. Introducing Silloscope our Sever, Desktop Monitoring and Endpoint Security Package Silloscope helps you meet many government regulations in 4 ways: 1. Compliance Tracking Compliance tracking intercepts security-related events from the Windows event log. 2. Real-Time Event Log Monitoring The core of our Server and Desktop Package is to monitor the security event log of Windows-based computers, we perform a variety of tasks including:
3. System Health and Performance Monitoring Depending on your specific compliance needs, many of the system health monitoring features supplement the compliance tracking and event log monitoring features. Server and Desktop Monitoring provides the following additional functionality to help you achieve compliance:
4. Security - Endpoint Protection Layered protection to keep endpoints safe from mass malware, targeted attacks, intrusion detection, and advanced persistent threats. Silloscope is not a guarantee that you will comply, but our powerful , real-time monitoring tools and reports will take some of the pain and complexity out of compliance. CONTACT US to learn more about Monitoring and Compliance!  How to Protect your Office, Company or Organization In recent months several of our clients have received email requests to wire transfer funds. This confidence scheme is highly targeted sending the fake wire transfer emails to employees working in the finance department of a company. How it works This con uses sophisticated social engineering to convince specific executives and other individuals with access to their company's accounts to initiate a wire transfer of large sums of money. The Deception In this attack, the scammer not only knows the target's name and email address, but also the name and email address of someone else in the company whom the target might trust. The scammers have registered email domains that are very similar to the recipients' (for example: xyzwigdets.com instead of xyzwidgets.com) and send the email from the fake domain. So, instead of coming from [email protected], the email comes from [email protected]. The scammers are betting that some people won't notice the slight difference in spelling and thus won't suspect anything. A Slow Con - No Dollar Amount at First This is an old-school trick we don't often see in email scams. The scammer cons the victim slowly, first gaining their trust and then moving in for the kill. In some of the emails, the first message is not only ordinary, it doesn't even request a specific amount of money. It merely asks to initiate a wire transfer today. The recipient, thinking it's coming from a co-worker who might ask for a wire transfer, replies to the scammer, who then engages in a brief email exchange, eventually asking for a specific amount. The scammer even confirms the money went through, probably to prevent the victim from becoming suspicious and reversing the transfer. Why doesn't our Spam filter catch these? This is a different type of threat. With its low-volume (only a handful of emails out of millions) and targeting of specific people, this dangerous campaign has few of the typical markers of spam. Why is this scam so successful? The people perpetrating these frauds frequently research employees’ responsibilities so they know who to target, and often gather information to try to make the wire transfer request as believable as possible. For example, they may research the executive’s schedule using public information or by making inquiries of the executive’s assistant with the goal of sending the fraudulent emails when the executive is out of town and cannot be easily reached for verification. Although some of the fraudulent requests are for millions of dollars, they can just as often be for smaller amounts. Since many companies have stricter controls (like dual approvals) for amounts over a certain dollar threshold, the scammers often submit requests for lower amounts hoping the looser controls will raise the success rate of their scam. If the scammer is successful in a preliminary request, they may continue to submit additional requests until the scam is detected. How to Protect Yourself and Your Company Implement a Strong Policy: Security and Fraud Prevention begins with a solid set of policies and procedures. A company policy should include confirmation on any wire transfers. Train everyone at your company based on your policy. Keep your staff up to date on the latest threats. Contact Us for more information. |
AuthorSilloway Support Team Archives
April 2024
Categories
All
|
Call today - 802 282-4255Silloway Networks offers Enterprise level support to Small and Medium Businesses in Rutland, Addison, Windsor and Bennington Counties. Employing highly-skilled technicians and developing partnerships with best-of-breed technology providers allows Silloway Networks to provide personalized technology solutions to enhance the operation of your business.
|
|
Website by Silloway Networks

 RSS Feed
RSS Feed