|
Silloway Networks is now proudly selling Lexmark imaging solutions!
Lexmark creates innovative imaging solutions and technologies that help customers print, secure and manage information with ease, efficiency and unmatched value. Drop us a line or give us a call to find out how we can help you find the right imaging device for your specific needs. Consulting on AI Use Cases in BusinessFacing a business challenge and feeling a bit lost? Fear not!
Our team of seasoned consultants is here to guide you. We’ll meticulously audit your business, identifying those pesky bottlenecks that hinder your growth. But that’s not all—we’ll go beyond diagnosis. Our expertise lies in AI solutions, and we’ll suggest tailored examples that can transform your business landscape. Whether it’s streamlining processes, enhancing customer experiences, or optimizing resource allocation, our AI Consulting Team have got you covered. Let’s turn those challenges into opportunities and propel your business forward! Summary: Our AI Consulting services offer expert guidance on AI use cases, helping businesses overcome challenges and unlock growth potential. Silloway Networks vCIO (Virtual Chief Information Officer)Understanding vCIO Services In today’s fast-paced business environment, staying on top of technology is crucial for success.
Enter Silloway Network's vCIO services, a rapidly growing trend among businesses of all sizes. A vCIO, or virtual Chief Information Officer, provides expert IT strategy and management without the hefty price tag of a full-time executive. By collaborating with your team, our vCIO creates a comprehensive IT roadmap aligned with your business goals. We handle tasks such as IT strategy development, cybersecurity, and vendor management. Beyond cost savings, our vCIOs anticipate issues, identify improvement opportunities, and ensure your IT infrastructure is agile and secure. Benjamin Franklin once said, “An ounce of prevention is worth a pound of cure.” This age old advice is easily applied to the digital world we live in today. Computers, applications and networks are under constant attack by hackers who are extremely motivated by big financial gains. An effective patch and vulnerability management program has the ability to stop most hackers dead in their tracks. It greatly reduces the risk associated with the exploitation of a neglected or un-patched computer system.
An ounce of prevention, in this case – patching computers and applications, is worth a pound of cure, in this case – the cost of responding to a cybersecurity incident or data breach. Year after year, we learn that the vast majority of successful cyber-attacks exploited unpatched computers and / or unpatched applications. What is even more interesting is that most of the patches for these compromised systems had been available to install for months, if not years prior to the cyber-attack. There is no doubt that the combination of routine vulnerability scanning and the timely installation of system patches will make it much more difficult for a hack to compromise your computer systems and information. There are seven steps you must take to build an effective patch and vulnerability management program:
It is common to see the responsibility of creating and maintaining a patch and vulnerability management program assigned to the Network Administrator or outsourced to a Third Party Service Provider. Patching equals prevention and remember – an ounce of prevention is worth a pound of cure. Patching is easy to do, inexpensive and is an incredibly effective cyber-security defense. Happy Patching. Sometimes, having access to the right data at the right time can enable life-saving decisions. If you don't believe so, just ask Monica, a Kenyan farmer who has to leverage water from a well in her back yard to irrigate her crops as well as provide her family with drinkable water. Due to climate change, rainy seasons have become more and more scarce, forcing her to carefully manage her water output depending on the weather patterns in her region. Watch this video to learn how solar-powered digital transformation and Microsoft Azure are empowering farmers like Monica with easily accessible, accurate data that allows them to effectively predict rainfall, control their irrigation systems, and increase yields.
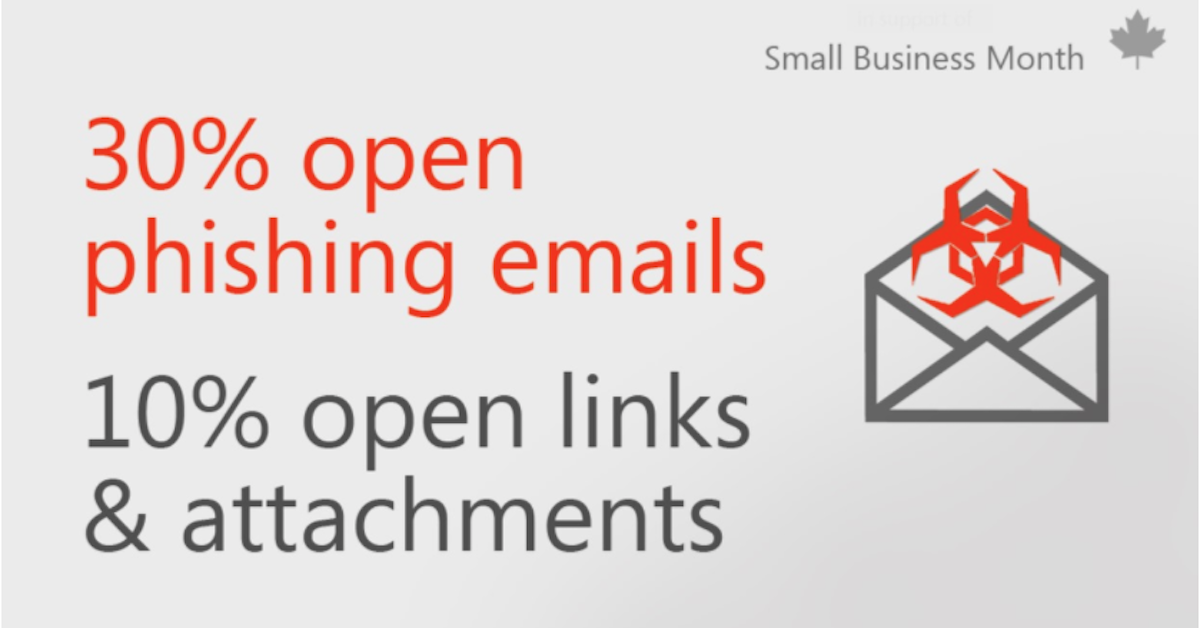
In this article , explore how small businesses can better assesses the risk(s) to them from criminal behavior, include phishing and other cyber-attacks. Then review the scope of activities you need to consider and a checklist you can follow. Categories All Today's diverse and intergenerational workforce is most productive when it has adequate channels to collaborate in a seamless and effective way.
There's a catch, however: teams are far more diverse and remote than ever before, and each organization requires its own distinct approach to digital collaboration. In other words, your workplace tools and applications must be customized based on your teams' diversity, location, and work methods. With this infographic, you'll learn about the three main characteristics that define our modern workplace and gain insight into what drives productivity and efficiency in today's organizations. After reading it, you'll have a better understanding of current trends and can keep these in mind when creating or modifying your organization's work environment. Online collaboration tools help employees with
At Silloway Networks, we specialize in helping businesses implement online productivity solutions and modernize their IT strategy. Contact us today to find out how we can help. Losing data because a device goes down is not an option. Cloud solutions like OneDrive for business can help you keep your data backed up and protected. With features like SSL encryption and the ability to set expiration dates on certain permissions, your data will be taken care of. Integrating new cloud solutions is tough for any business. Learn More
That's why we're here to take care of you. Contact Silloway Networks today to find out more on how we can help. With many employees suddenly working from home, there are things an organization and employees can do to help remain productive without increasing cybersecurity risk. While employees in this new remote work situation will be thinking about how to stay in touch with colleagues and coworkers using chat applications, shared documents, and replacing planned meetings with conference calls, they may not be thinking about cyberattacks. Business owners, ED's and admins need to look urgently at new scenarios and new threat vectors as their organizations become a distributed organization overnight, with less time to make detailed plans or run pilots. Based on our experiences working with customers who have had to pivot to new working environments quickly, I want to share some of those best practices that help ensure the best protection. What to do in the short—and longer—termEnabling official chat tools helps employees know where to congregate for work. Whichever software you pick, provision it to users with Azure Active Directory (Azure AD) and set up single-sign-on, and you won’t have to worry about download links getting emailed around, which could lead to users falling for phishing emails. You can secure access to cloud applications with Azure AD Conditional Access, protecting those sign-ins with security defaults. Remember to look at any policies you have set already, to make sure they don’t block access for users working from home. Azure AD Application Proxy publishes on-premises apps for remote availability, and if you use a managed gateway, today we support several partner solutions with secure hybrid access for Azure AD. While many employees have work laptops they use at home, it’s likely organizations will see an increase in the use of personal devices accessing company data. Using Azure AD Conditional Access and Microsoft Intune app protection policies together helps manage and secure corporate data in approved apps on these personal devices, so employees can remain productive. Intune automatically discovers new devices as users connect with them, prompting them to register the device and sign in with their company credentials. You could manage more device options, like turning on BitLocker or enforcing password length, without interfering with users’ personal data, like family photos; but be sensitive about these changes and make sure there’s a real risk you’re addressing rather than setting policies just because they’re available. You’ve heard me say it time and again when it comes to multi-factor authentication (MFA): 100 percent of your employees, 100 percent of the time. The single best thing you can do to improve security for employees working from home is to turn on MFA. If you don’t already have processes in place, treat this as an emergency pilot and talk to our Silloway Support Team to implement MFA. Longer term, I recommend Azure Information Protection to find and label the most critical data so you can track and audit usage when employees work from home. We must not assume that all networks are secure, or that all employees are in fact working from home when working remotely. Track your Microsoft Secure Score to see how remote working affects your compliance and risk surface. Use Microsoft Defender Advanced Threat Protection (ATP) to look for attackers masquerading as employees working from home. How to help employeesAs more organizations adapt to remote work options, supporting employees will require more than just providing tools and enforcing policies. It will be a combination of tools, transparency, and timeliness.
Remote workers have access to data, information, and your network. This increases the temptation for bad actors. Warn your employees to expect more phishing attempts, including targeted spear phishing aimed at high profile credentials. Now is a good time to be diligent, so watch out for urgent requests that break company policy, use emotive language and have details that are slightly wrong—and provide guidance on where to report those suspicious messages. Establishing a clear communications policy helps employees recognize official messages. For example, video is harder to spoof than email: an official channel like Microsoft Stream could reduce the chance of phishing while making people feel connected. Streaming videos they can view at a convenient time will also help employees juggling personal responsibilities, like school closures or travel schedule changes. Transparency is key. Some of our most successful customers are also some of our most transparent ones. Employee trust is built on transparency. By providing clear and basic information, including how to protect their devices, will help you and employees stay ahead of threats. For example, help employees understand why downloading and using consumer or free VPNs is a bad idea. These connections can extract sensitive information from your network without employees realizing. Instead, offer guidance on how to leverage your VPN and how it’s routed through a secure VPN connection. Employees need a basic understanding of conditional access policies and what their devices need to connect to the corporate network, like up-to-date anti-malware protection. This way employees understand if their access is blocked and how to get the support they need. Working from home doesn’t mean being isolated. Reassure employees they can be social, stay in touch with colleagues, and still help keep the business secure. |
AuthorSilloway Support Team Archives
April 2024
Categories
All
|
Call today - 802 282-4255Silloway Networks offers Enterprise level support to Small and Medium Businesses in Rutland, Addison, Windsor and Bennington Counties. Employing highly-skilled technicians and developing partnerships with best-of-breed technology providers allows Silloway Networks to provide personalized technology solutions to enhance the operation of your business.
|
|
Website by Silloway Networks





 RSS Feed
RSS Feed